ezbroke
解法
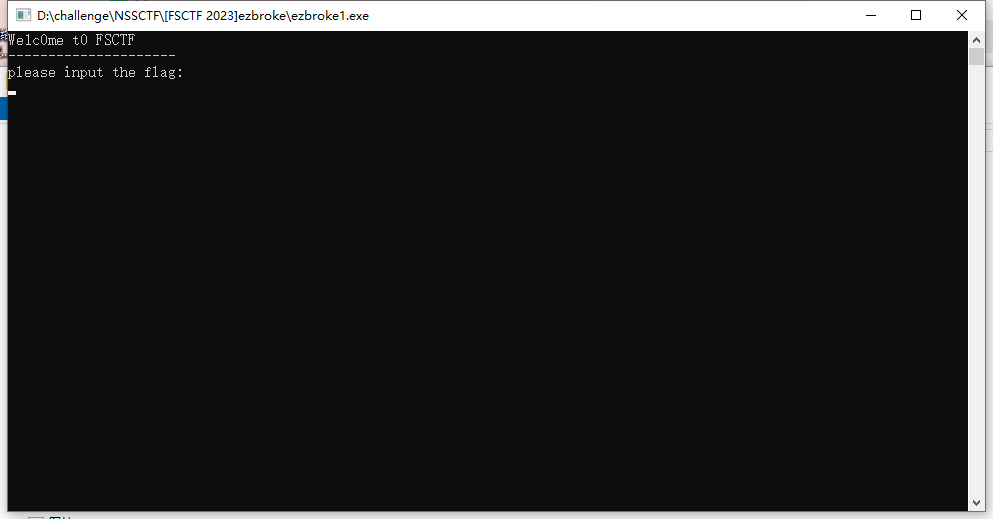
下载下来 一个exe,点开看看
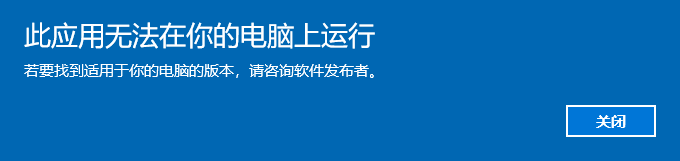
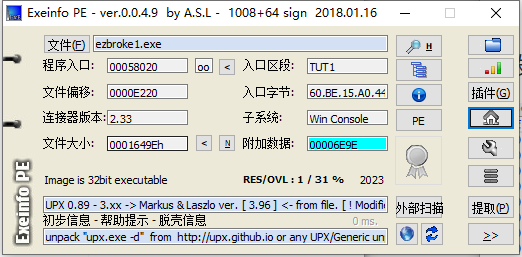
无法运行,exeinfo看看
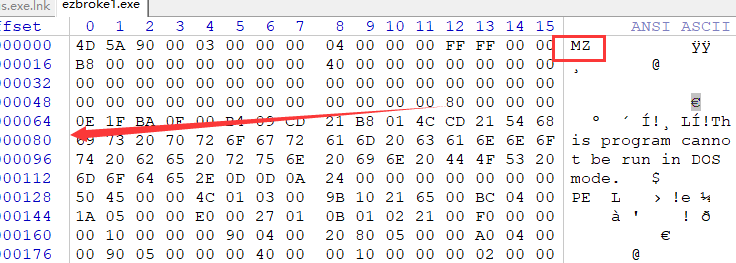
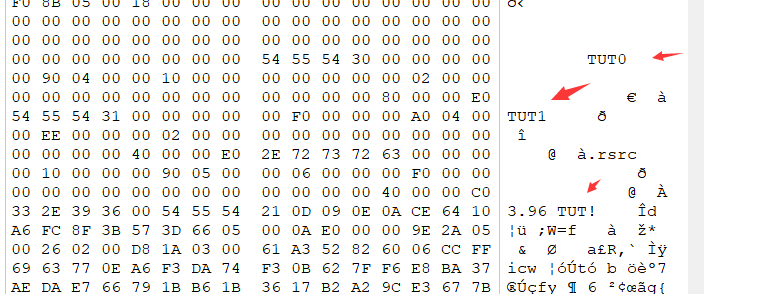
长这样,可能损坏了,winhex看看
发现dos头和pe的文件偏移都有问题,修改。
发现可以正常打开了
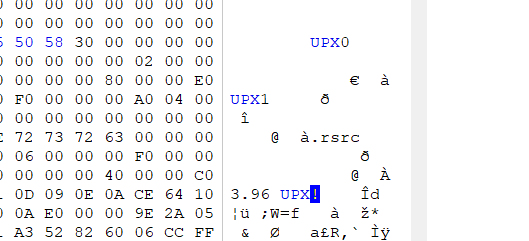
但是发现仍然有upx壳
脱壳,发现失败了
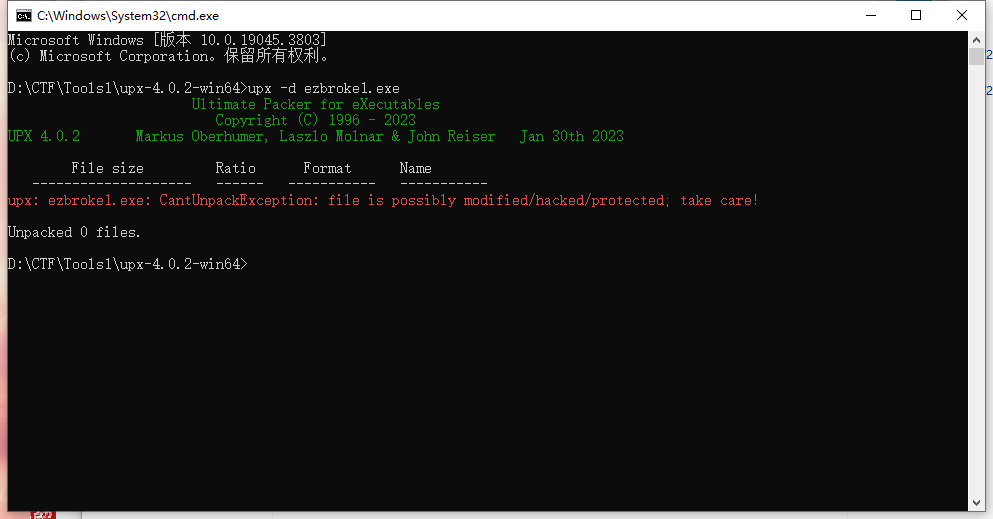
继续winhex看看,发现都修改了
修改后
再去脱壳,成功
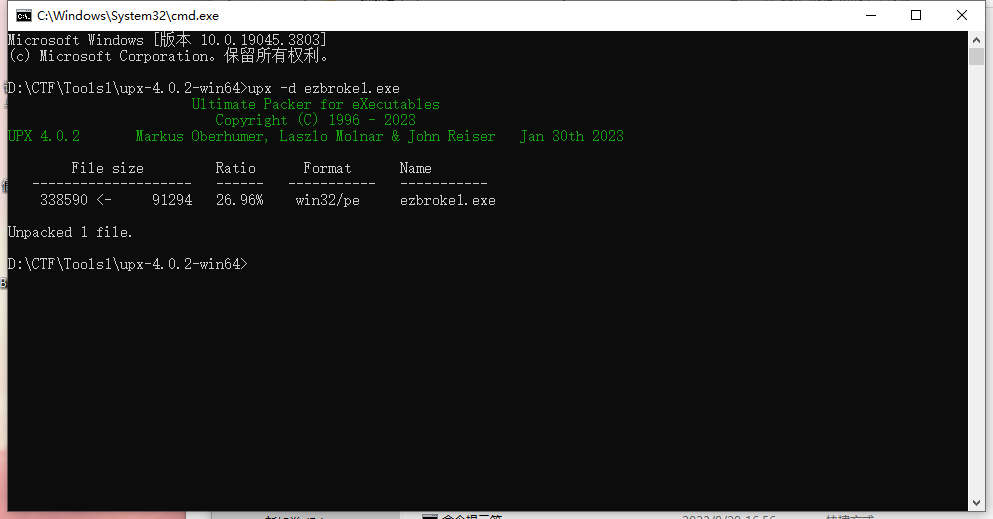
打开ida32,发现好像是个VM题奥
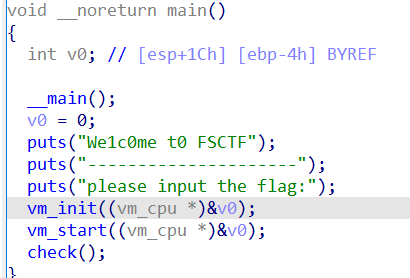
不过还是比较友好,直接给了我有啥操作
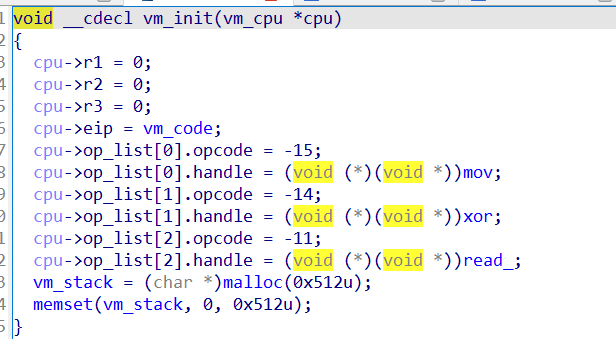
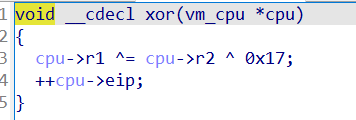
一个一个看过之后,应该就是这了,异或0x17
然后进check比较
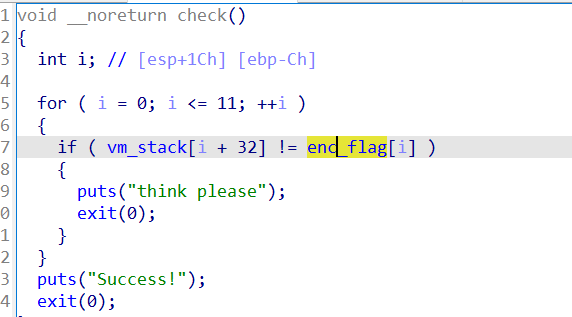
所以逆向思路就是,把encflag先dump出来,然后再异或回去
Enc = [
0x51, 0x44, 0x54, 0x43, 0x51, 0x6C, 0x4E, 0x27, 0x62, 0x37,
0x64, 0x62, 0x74, 0x74, 0x72, 0x64, 0x64, 0x71, 0x62, 0x26,
0x26, 0x6E, 0x37, 0x75, 0x65, 0x27, 0x7C, 0x24, 0x37, 0x7A,
0x6E, 0x37, 0x67, 0x65, 0x27, 0x63, 0x24, 0x74, 0x63, 0x26,
0x27, 0x79, 0x36, 0x36, 0x36, 0x6A, 0x00
]
cFlag = ""
for i in range(len(Enc)):
cFlag += chr(Enc[i] ^ 0x17)
print(cFlag)
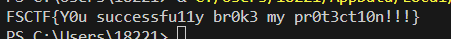
出了